The abandonment rate in the financial industry can be reduced — but only by addressing the underlying causes and redesigning digital experiences with real user needs in mind.
The optimal digital customer verification process
Nowadays, with the use of the Internet, we are used to interacting with each other through screens. The progress that this has meant, and the advantages that the digital world offers us, is quite notorious. But it is not all comfort and benefits, there are also a series of threats that it is important to control and try to eliminate.
When conducting digital transactions and identity verification processes remotely, security measures that verify a person’s identity are essential. The key is to gather sufficient evidence, which can range from traditional identification documentation to real-time video assurance.
In this post we show you some of the methods for verifying a digital identity. These can be used separately, or in combination with each other, to perfectly tailor the solution to your company’s needs.
Providing the customer with an electronic ID
Electronic identification allows you to ensure that your customers are who they say they are when they are online. In addition to enabling online authentication across multiple platforms and services, eIDs can also give individuals the ability to sign electronic documents with a legally binding digital signature.
Electronic IDs can provide the level of identity assurance needed to satisfy the strictest AML (Anti Money Laundering) and KYC (Know Your Customer) requirements, giving service providers everything they need to confirm that their customers are who they say they are.
Identification processes may differ from provider to provider, but generally, when electronic identification is established, customers are required to share it:
- Personal identity attributes, e.g. their full name, date of birth, address.
- Proof of their identity by showing or sending paper identity documents.
The e-ID provider then verifies the customer’s identity by means such as video identification or biometric personal identification, which are checked against identity documents such as a passport or driving licence.
Once the electronic ID has been verified, it is verified wherever it is used. Using an electronic identity document from a trusted service provider to verify digital identities means that, as a business, you do not need to verify the identities yourself.
Obtaining evidence of your customer’s identity documents
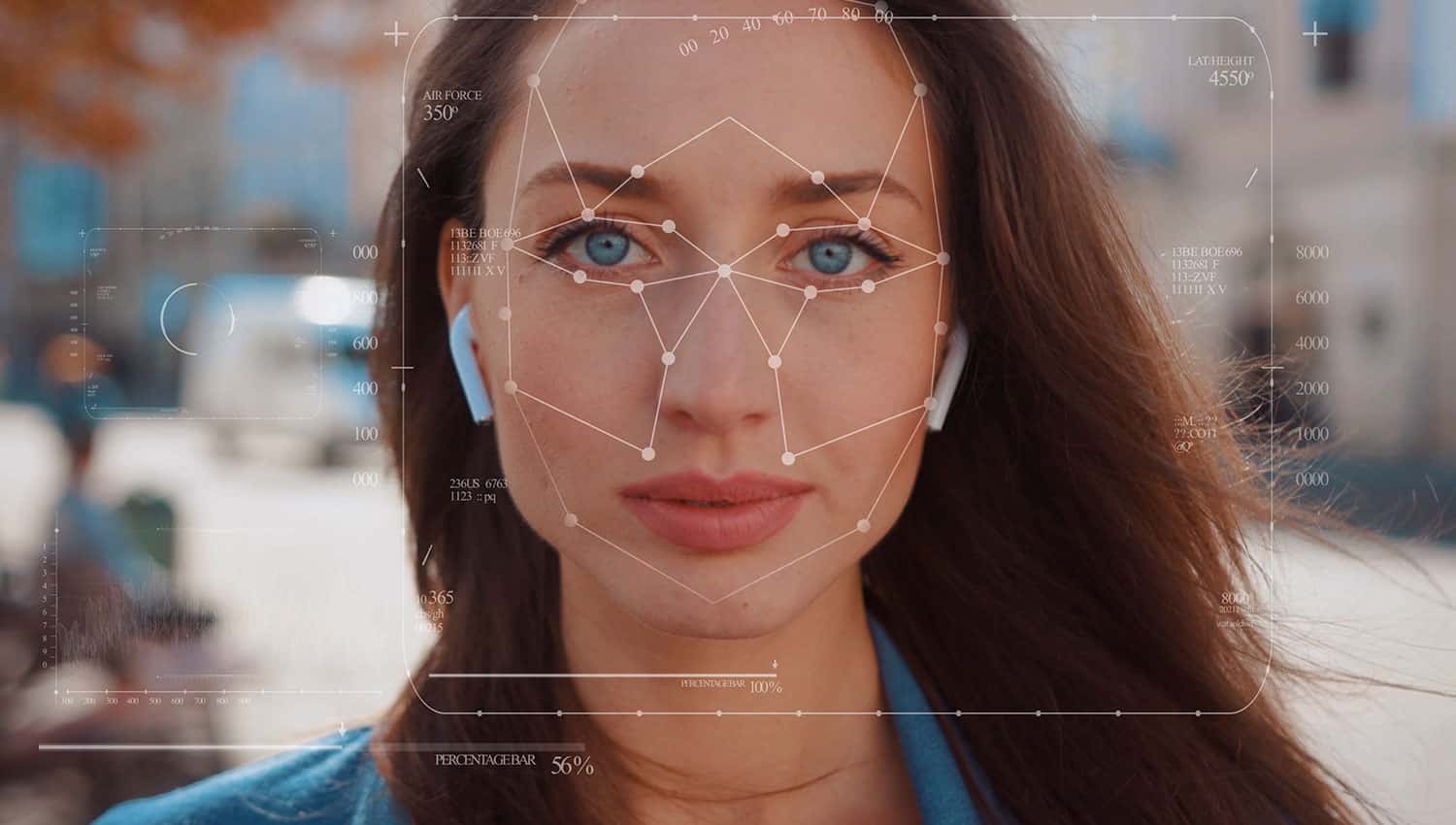
Identity document verification requires users to scan or take a photo of an identity document (passport, national identity card, residence permit or driver’s licence). Alternatively, users can hold their ID document up to their phone, which reads the information on the document using NFC (Near Field Communication). This will prove to a high degree that the user is in possession of the original ID document, and is not a copy of it. Some providers will have ID document scanning, facial recognition, live video detection, and other forms of ID verification. This ensures higher levels of security, and builds trust between the customer and your business.
Customer verification
Some digital identity verification providers may provide various record searches. These can be used to verify information provided by the user, including postal address, or to provide additional information to both users and organisations.
The problem is that there are multiple sources of this information, such as the electoral roll or central government records. Or, not all customers will be registered and some may be registered with outdated details. Register searches are often integrated with other methods of digital identity validation.
Phone number and email for customer authentication
There are several easy and simple authentication methods involving mobile phone numbers and email addresses. After a customer has signed up for your service, you can validate that the user is in possession of the phone or email account by asking them to confirm their number or email address. However, this only proves that you have access to an email account or phone number, not who the user is.
Video identification service for customer authentication
Face matching provides an additional layer of trust for the authentication process. It can be used before or after the ID verification step. In this step, a self-portrait or selfie of the user, as well as images taken from the uploaded ID documents, are compared to see if they match. The customer can even be asked to take a photo of his or her passport or photos from various angles of the customer with the passport open. This proves that the customer is in possession of the ID.
In addition, proof of life can also be carried out, which asks users to perform a random sequence of actions, which can ensure verification of the identity of remote customers. Video identification thus becomes both secure and complete.
User abandonment in verification processes must be avoided.
There is a challenge in using all methods of identity verification, because as the level of security and reliability goes up, the user experience (UX – User experience) can go down. People get frustrated if it takes too long to go through the process, so it is a good idea not to do everything up front or at once. Start with something simple and ask for more evidence later in the process in a sequential way. Carry out checks as the user is immersed in another part of the process and get the most technical and legal certainty without undermining the customer experience.